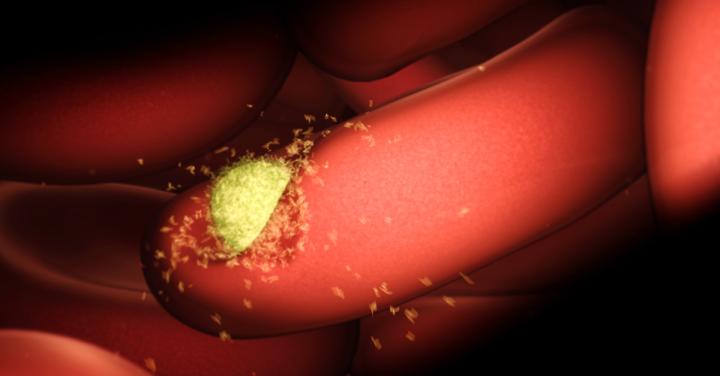
St. Jude Children's Research Hospital investigators have demonstrated that comprehensive genomic sequencing of all pediatric cancer patients is feasible and essential to capitalize on the lifesaving potential of precision medicine. Results from the St. Jude Genomes for Kids study appear online today in the journal Cancer Discovery. 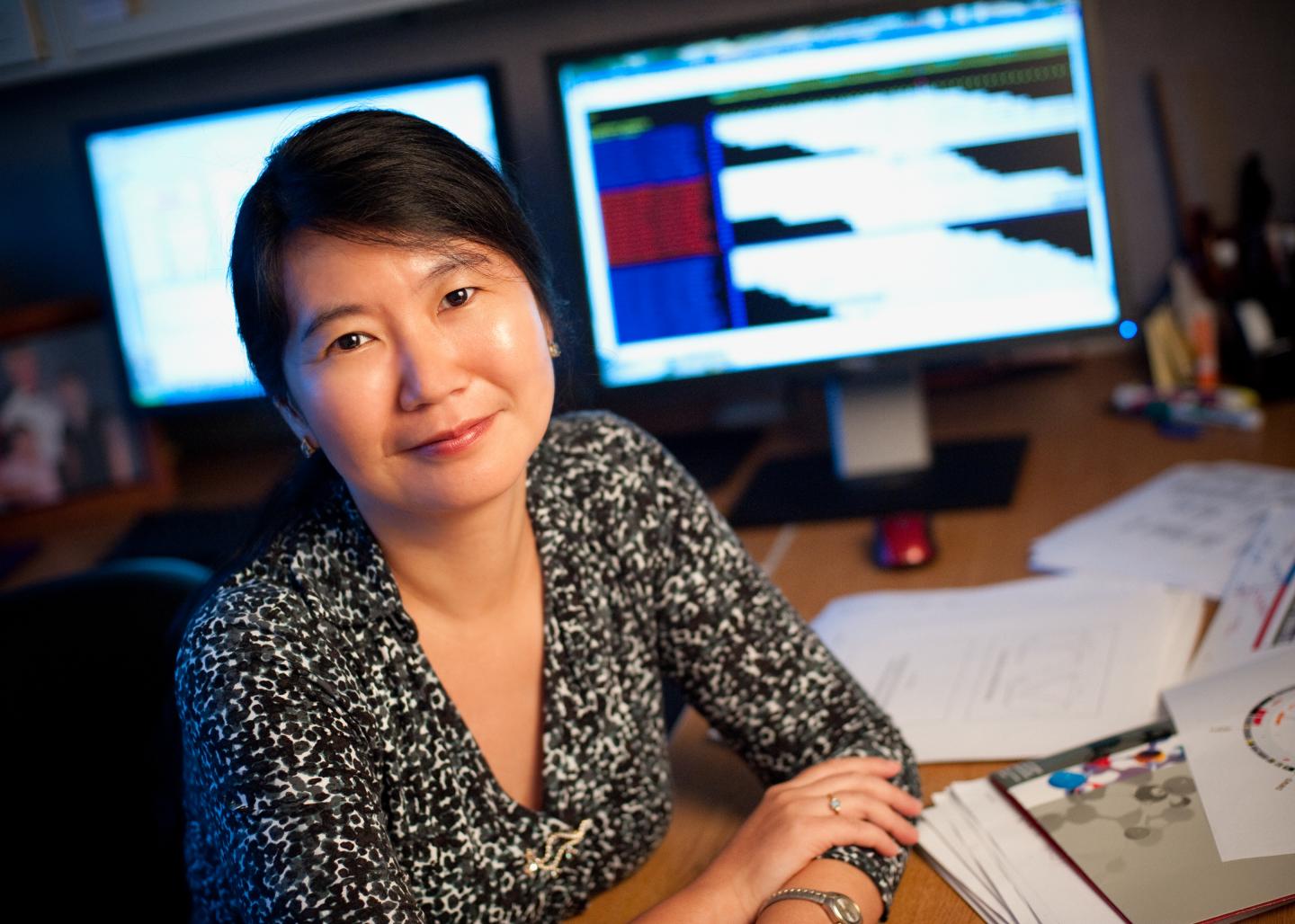
Whole-genome and whole-exome sequencing of germline DNA were offered to all 309 patients who enrolled in the study. Whole-genome, whole-exome, and RNA sequencing of tumor DNA were carried out for the 253 patients for whom adequate tumor samples were available.
Overall, 86% of patients had at least one clinically significant variation in tumor or germline DNA. Those included variants related to diagnosis, prognosis, therapy, or cancer predisposition. Researchers estimated that 1 in 5 patients had clinically relevant mutations that would have gone undetected using standard sequencing methods.
"Some of the most clinically relevant findings were only possible because the study combined whole-genome sequencing with whole-exome and RNA sequencing," said Jinghui Zhang, Ph.D., St. Jude Department of Computational Biology chair and co-corresponding author of the study.
Every tumor is unique. Every patient is unique.
Comprehensive clinical sequencing that includes whole-genome, whole-exome, and RNA sequencing is not widely available. But as the technology becomes less expensive and accessible to more patients, researchers said comprehensive sequencing will become an important addition to pediatric cancer care.
"We want to change the thinking in the field," said David Wheeler, Ph.D., St. Jude Precision Genomics team director, and a co-author of the study. "We showed the potential to use genomic data at the patient level. Even in common pediatric cancers, every tumor is unique, every patient is unique.
"This study showed the feasibility of identifying tumor vulnerabilities and learning to exploit them to improve patient care," he said.
Tumor sequencing guided the change in treatment for 12 of the 78 study patients for whom the standard of care was unsuccessful. In four of the 12 patients, the changes stabilized disease and extended patient lives. Another patient, one with acute myeloid leukemia, went into remission and was cured by blood stem cell transplantation.
"Through the comprehensive genomic testing in this study, we were able to clearly identify tumor variations that could be treated with targeted agents, opening doors for how oncologists manage their patients," said co-corresponding author Kim Nichols, M.D., St. Jude Cancer Predisposition Division director.
Additional findings and details
Genomes for Kids enrolled patients between August 2015 and March 2017.
Eighteen percent of patients carried germline variations in one of 156 known, cancer-predisposition genes.
Almost two-thirds of the germline variations identified would not have been detected based on current screening guidelines.
Next steps
Genomes for Kids helped launch the hospital's clinical genomics program, which has enrolled about 2,700 cancer patients to date.
Meanwhile, data generated through the Genomes for Kids study are available at no cost to the international research community. By sharing the data, St. Jude aims to speed advances in understanding and treatment of pediatric cancer. The data are available in St. Jude Cloud.
"Even the most treatable cancers are not curable in all patients. For example, relapse remains the leading cause of death for the most common childhood cancer, acute lymphoblastic leukemia," Nichols said. "Being able to understand and predict which patients will respond to treatment and which won't require collecting comprehensive genomic data on all patients."
 How to resolve AdBlock issue?
How to resolve AdBlock issue?